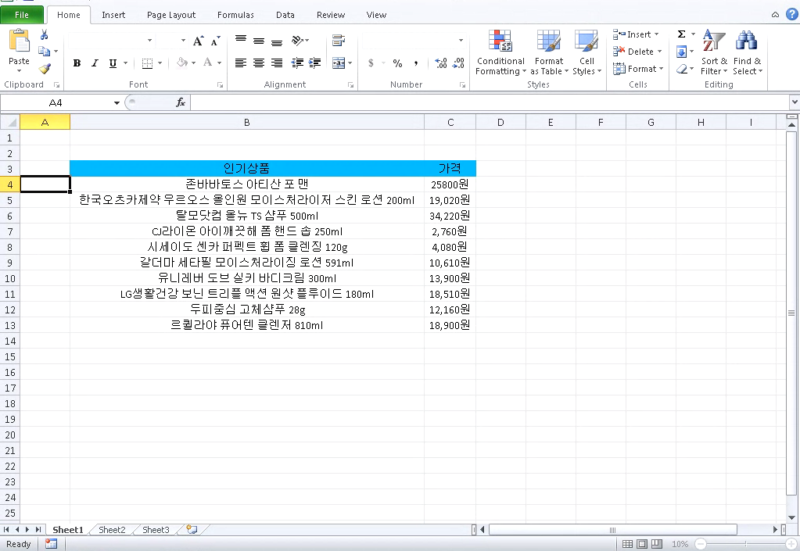
Enlarge / A screenshot of the malicious Excel document spreading a Flash zeroday. (credit: Talos)
An increasingly sophisticated hacking group is exploiting a zero-day vulnerability in Adobe’s Flash Player that lets them take full control of infected machines, researchers said Friday.
The critical, use-after-free vulnerability, which is indexed as CVE-2018-4877, resides in the latest version of the widely installed Flash, researchers from Cisco Systems’ Talos group said in a blog post. Adobe said separately that versions earlier than current Flash 28.0.0.137 are also susceptible. The vulnerability came to light on Wednesday when South Korea’s CERT issued an advisory warning that attack code was circulating in the wild that exploited the zeroday flaw.
Talos said the exploit is being distributed through a Microsoft Excel document that has a malicious Flash object embedded into it. Once the SWF object is triggered, it installs ROKRAT, a remote administration tool Talos has been tracking since January 2017. Until now, the group behind ROKRAT—which Talos calls Group 123—has relied on social engineering or exploits of older, previously known vulnerabilities that targets hadn’t yet patched. This is the first time the group has used a zeroday exploit.
